Market Infrastructure Analysis
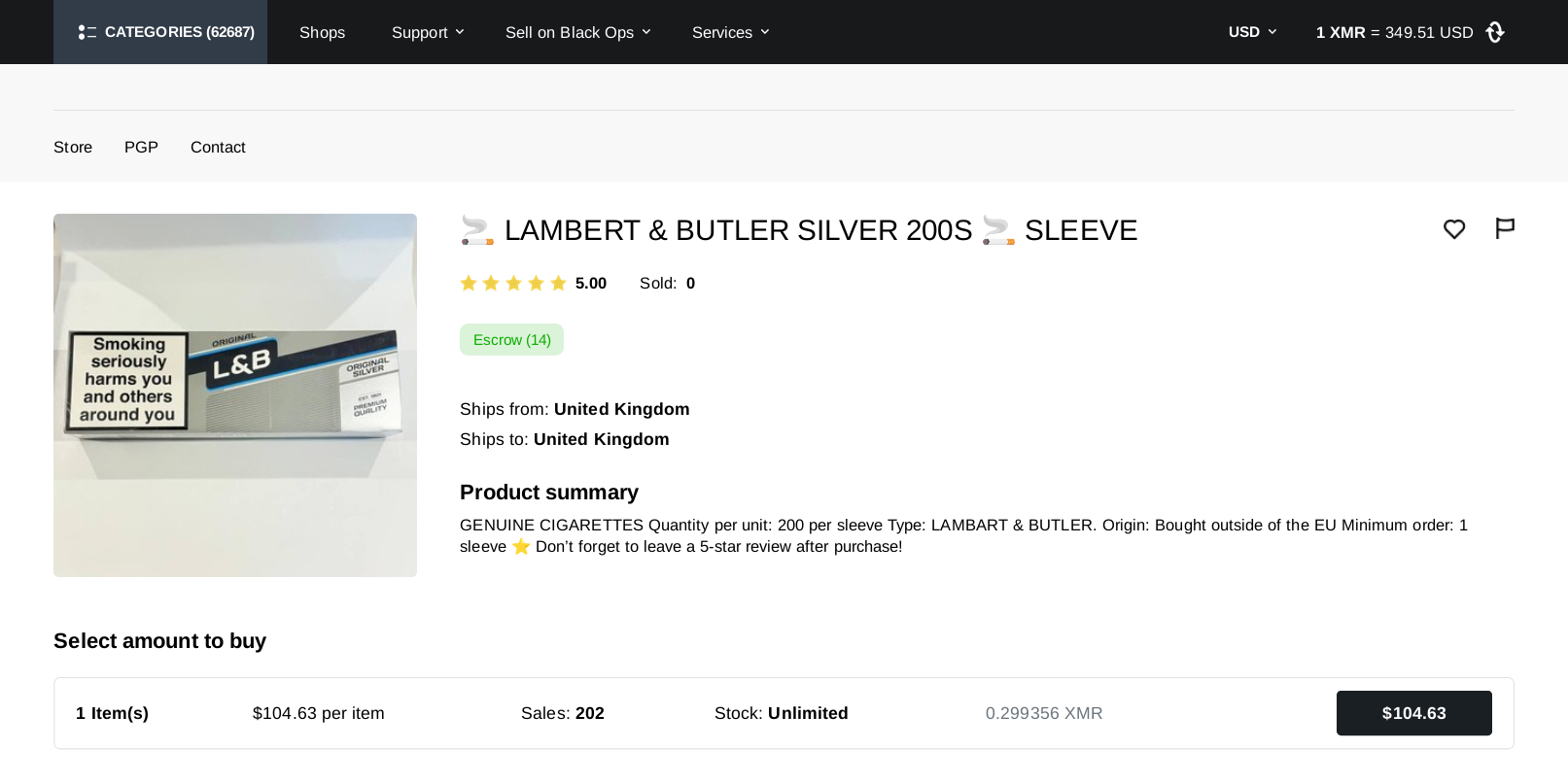
Black Ops Market Verified represents a specific iteration of darknet marketplace architecture focused on minimizing user footprint through enforced Monero (XMR) integration and strict PGP (Pretty Good Privacy) authentication standards.
Unlike earlier generations of onion services that relied on centralized Bitcoin wallets, the blackops market infrastructure utilizes a hybrid escrow system designed to reduce server-side liability. This page serves as a technical log of the platform's operational history, verified mirror rotation schedules, and security feature set.
Technical Specs
- Network: Tor / I2P
- Currency: XMR (Monero)
- Encryption: PGP 4096-bit
- Scripting: No-JS
- Escrow: Multisig
Operational Timeline
Mainnet Launch
Initial deployment of the blackops market onion service. The codebase was established with a strict "Monero-Only" policy to mitigate blockchain analysis risks associated with transparent ledgers.
Infrastructure Hardening
Implementation of advanced DDoS protection verification screens (see Fig 1.0 below) and introduction of rotating mirror architecture to maintain uptime during network stress tests.
PGP Mandatory Enforcement
The platform updated its registration protocol to require PGP 2FA for all accounts, eliminating password-only access. This shift aligned with industry-standard security practices.
Interface Architecture
Visual documentation of the user experience and security gates.
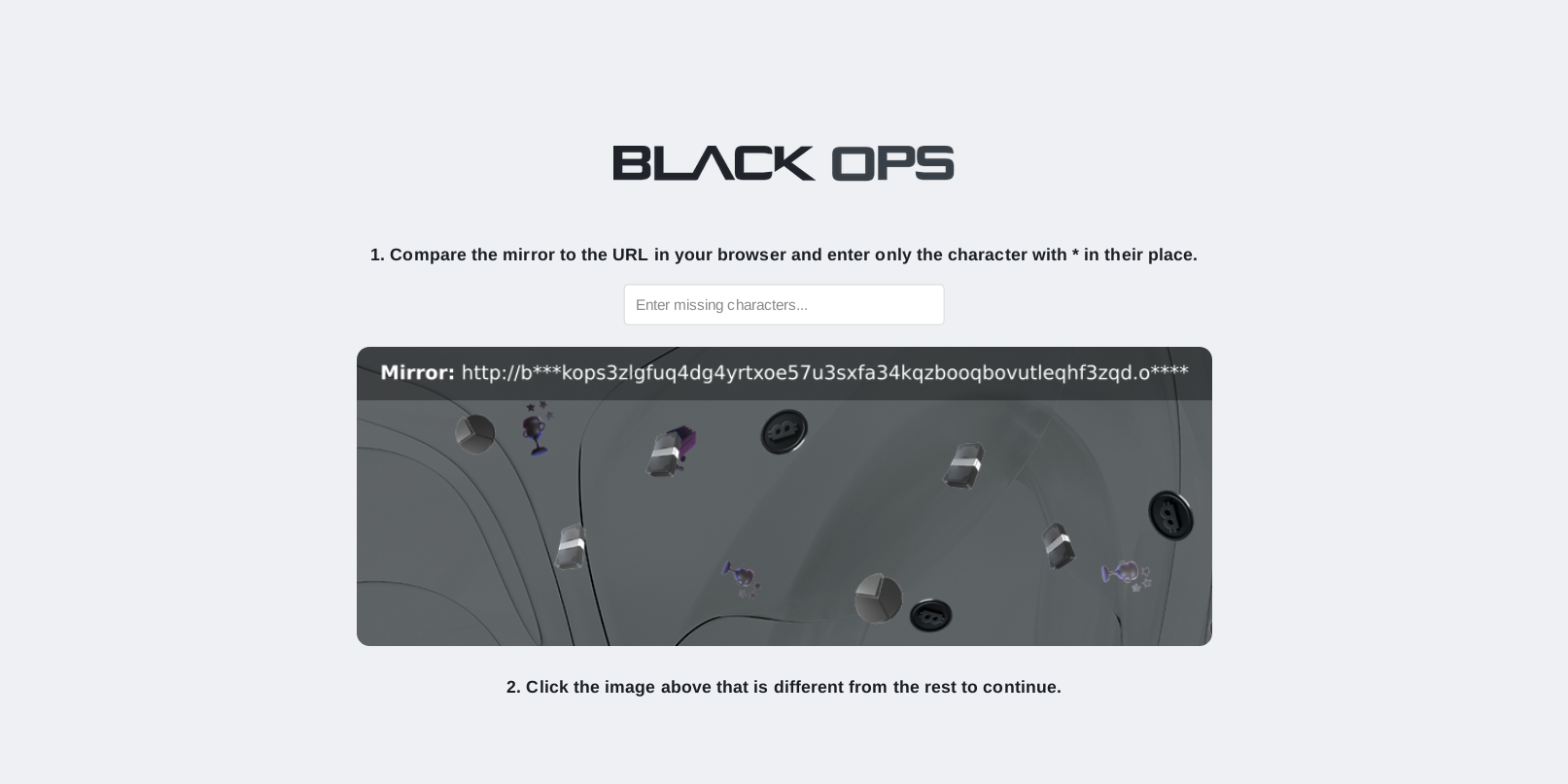
DDoS Mitigation
Clock-based captcha system prevents automated botnet indexing.
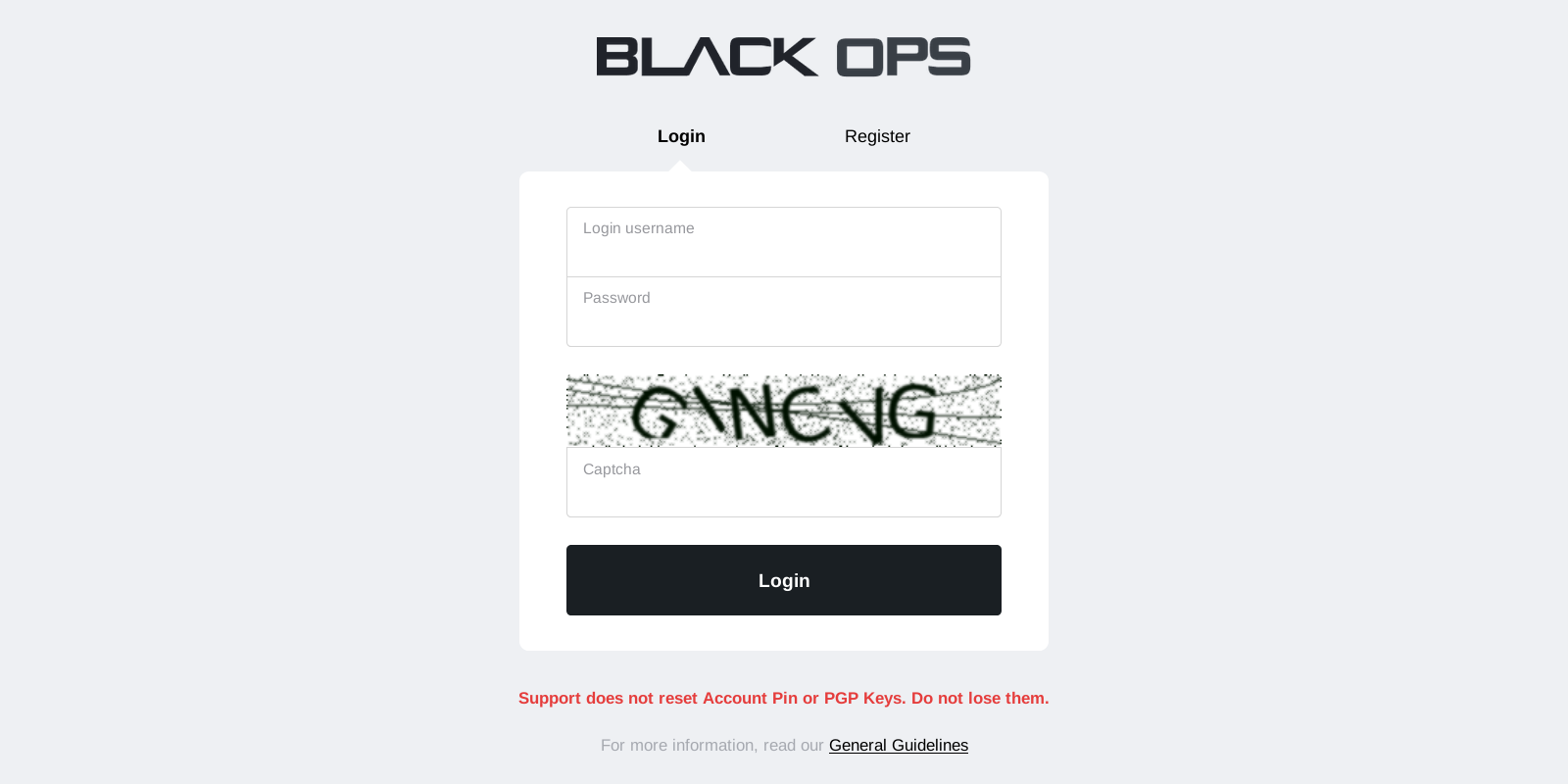
Encrypted Login
Decentralized authentication requiring private key decryption.
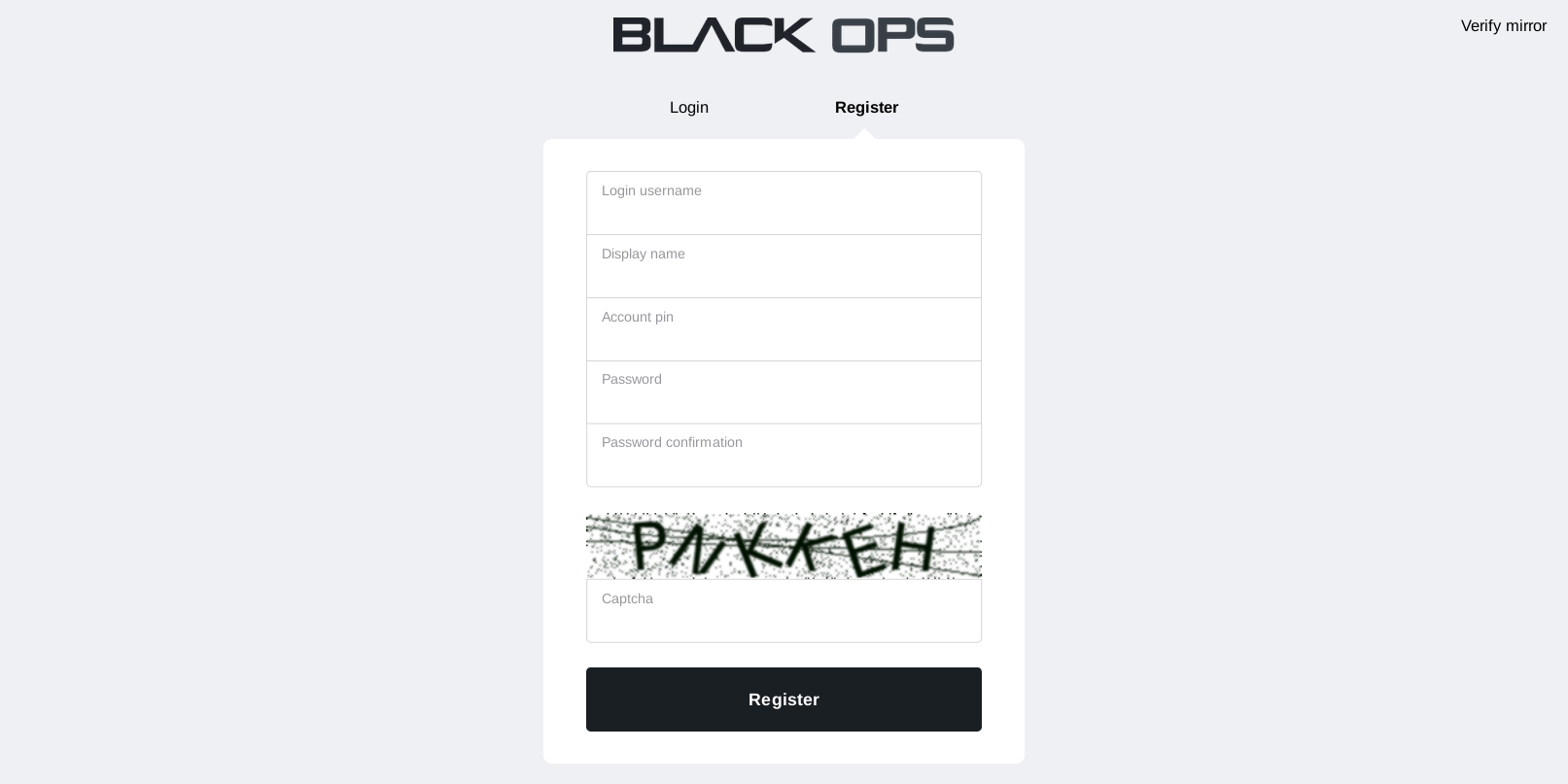
Identity Protection
Registration requires zero PII (Personally Identifiable Information).
Utilitarian UI
High-contrast, text-heavy interface optimized for Tor latency.
Security Protocol Observations
Mnemonic Recovery
Black Ops Market utilizes a 12-word mnemonic seed phrase system for account recovery. This ensures that even if local hardware is compromised, access relies on information stored solely in the user's possession, not on a centralized email server.
Mirror Verification
To combat phishing, the platform signs all valid execution mirrors with a master PGP key. Our research group monitors these signatures daily. A blackops market url is only considered "verified" if it matches the signed list broadcasted on the main canary.